There was another major crypto hack that started on Tuesday, August 2, 2022. The second large one in the span of two days. This time it was on the Solana network.
In the early hours, the cause and origin of the attack was unknown. At first there was mass confusion about how exactly this was happening. Then there was a mad scramble to spread the news and as users attempted to determine if their wallets might be drained next.
Reports circulating that $5 million – $8 million worth of SOL (Solana’s native cryptocurrency), more than 300 Solana-based tokens, and some NFTs had been drained from roughly 8,000 wallets.
A source of great concern was the news that some of the compromised addresses had been inactive for an extended period of time, indicating that this exploit might go back quite a way.
Blockchain security experts quickly honed in on the possibility of a supply-chain attack rather than a bug in the core Solana code. Supply-chain attacks are a type of cyberattack that target third-party vendor access points rather than the root organization.
Solana came to the same conclusion. “Engineers … continue to investigate the root cause of an incident that resulted in approximately 8,000 wallets being drained,” Austin Federa, head of communications at the Solana Foundation, told Fortune. “This does not appear to be a bug with Solana core code, but in software used by several wallets popular among users of the network.”
Who was impacted?
Unlike most recent high dollar hacks that target a single organization, this attack impacted thousands of wallets. The vast majority of the wallets that were impacted were third-party Solana “hot” wallets (wallets connected to the Internet). Most reported were hot wallets Slope, Phantom, and TrustWallet.
How did this happen?
In a blog post on Wednesday, August 3, 2022, the security firm Elliptic posted, “The root cause is still not clear, but it appears to be due to a flaw in certain wallet software – rather than in the Solana blockchain itself.”
That assertion later proved to be correct. As users and security professionals dug into the data a major flaw in the Slope wallet was discovered. The wallet had been logging and broadcasting, in clear text, the mnemonic seed phrases of users wallets.
Seed phrases are used to generate the private key for the address, and private keys grant full control of the wallet address. Once someone has a seed phrase / private key they are the de facto owner of the address and can drain the wallet by signing transactions to move crypto and NFTs. Those addresses are now all compromised and can never be safely used again.
On Twitter the user MoonRank outlined how the attack happened with a simple Tweet containing just this image.
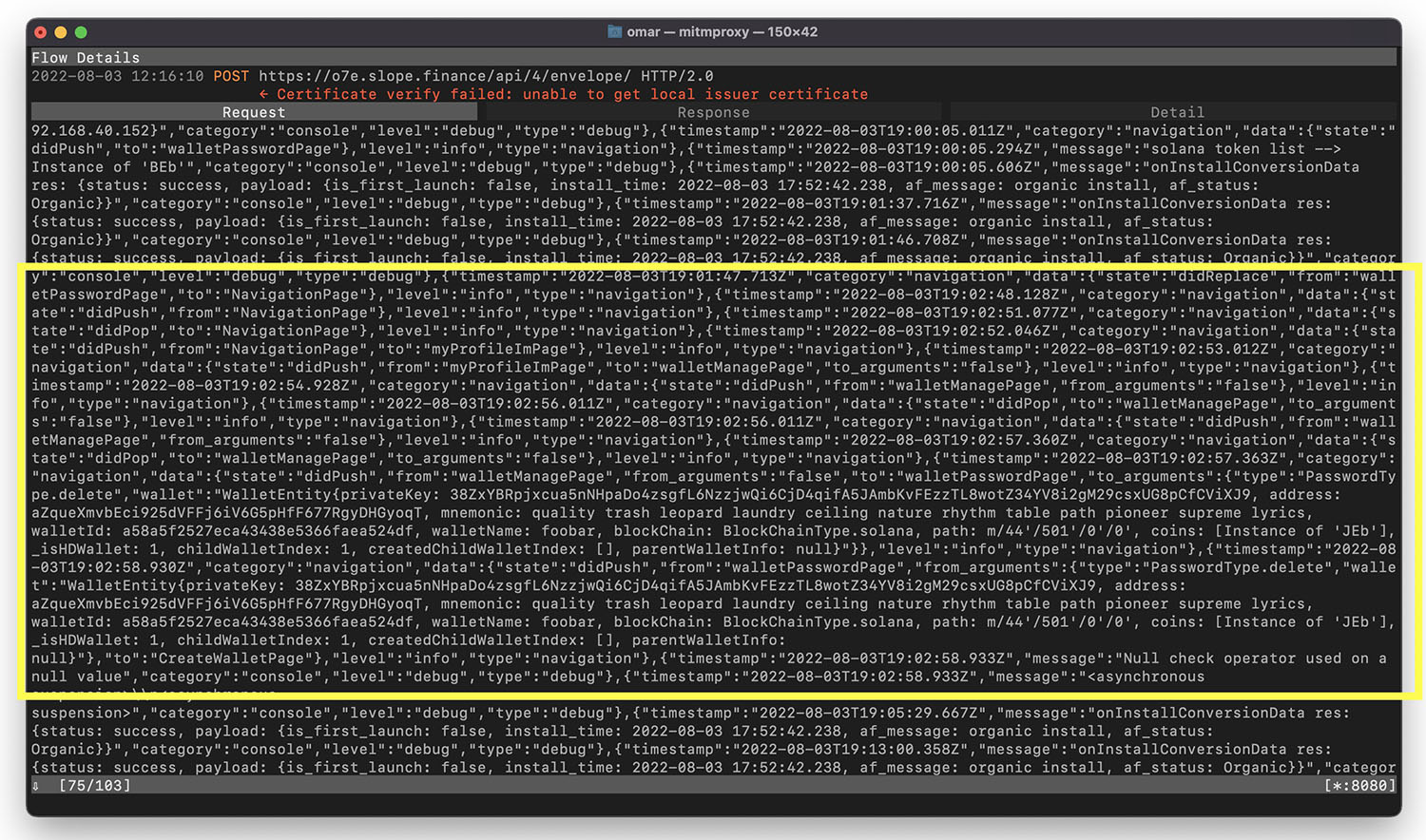
Other users quickly confirmed in the comments that this image showed the Slope wallet was incorrectly and egregiously sending user’s private keys and seed phrases in clear type for anyone to see.
The data was replicated by another user on Twitter, MiamiVice_sol who went into a bit more detail in this detailed thread.
What about those other wallets?
It appears that all of those compromised addresses originated on the Slope. Impacted users on TrustWallet and Phantom had imported their wallet after originally created their addresses on Slope.
Response from Slope
In a Medium article on August 3, 2022, Slope initially provided very poor guidance to their users suggesting, “Create a new and unique seed phrase wallet, and transfer all assets to this new wallet. Again, we do not recommend using the same seed phrase on this new wallet that you had on Slope.” Unfortunately, due to the nature of the vulnerability within their wallet, this would have resulted in a false sense of security as those new addresses would also have been broadcast in the clear.
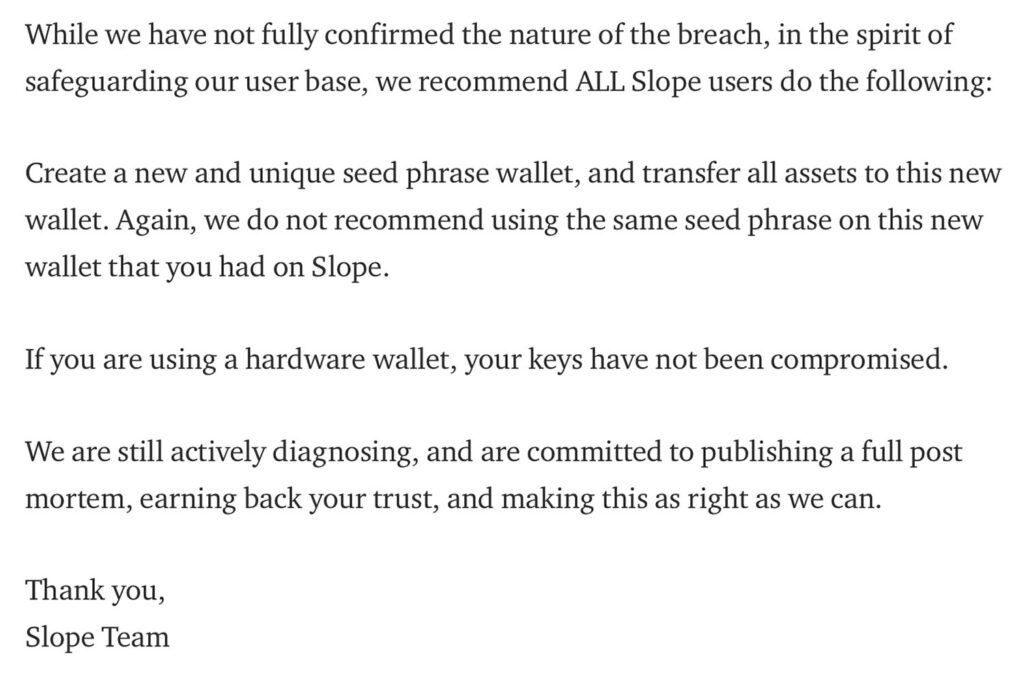
Since that post, Slope has not updated either the original article or posted new guidance to impacted users on Medium.
What should Solana users do?
Anyone who created a wallet on Slope should immediately migrate everything on it away to a new address. This includes TrustWallet and Phantom users who originally created addresses on Slope and then imported their addresses to a new wallet provider.
It is recommended that users move to a hardware wallet. Hardware wallets, such as a Ledger, were not impacted since this was a private key leak by a single hot wallet. Hardware wallets keep their private keys entirely offline, preventing this kind of exploit.
Learn more about setting up a hardware wallet here.