with editing by taxil
What is signing?
Signing is a cryptographic operation involving a message and your private key. You use your private key to “sign” a message, producing a special signature which proves that the wallet actually signed the message. The specifics of how it signs are beyond the scope of this article, but the key points are as follows:
- The signature is unique to the private key and the message it signs.
- The public key, and thus your address, can be derived given the signature and the message.
- This is how the blockchain verifies your transactions are signed by you and not forged.
How does signing a transaction work?
When MetaMask pops up the “confirm transaction” screen and you click to confirm, it takes the parameters of the transaction (the value if any, recipient address, etc.) and turns it into a message which is signed when you press confirm (and, we hope, double confirm on your hardware wallet immediately afterwards). MetaMask then broadcasts your transaction with the signature attached over the Ethereum network.
So do all signatures create a valid transaction (like if collabland asks me to sign a message)?
MetaMask uses a few different signing methods such as “personal_sign” which prepends messages with a string like “Ethereum Signed Message”. As mentioned before, signing involves using your private key and a message to create a signature – the blockchain needs transaction messages to be a certain format in order to be valid. By adding the “Ethereum Signed Message” at the front, the message is not of the correct format, and thus will not be validated. This way, even if a transaction is passed as a message, the signature would be different (since if the message is different, the signature is too), meaning it would not be verified as a valid transaction.
However, do not get complacent! Just because it can’t be used as a valid transaction signature, there are plenty of other types of attacks that don’t use transaction signatures, e.g. making you sign OpenSea listing orders.
Things to watch out for
Here is a recent example of a malicious site using the eth_sign method. This does NOT prepend the string, and so can be used to sign transactions, even though it doesn’t show any transaction confirmation screen!
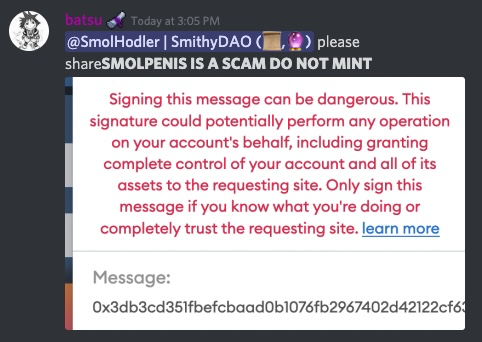
The message shown here contains a long hex string, almost certainly an encoded transaction it wants you to sign. You have no idea what that transaction is capable of! Note MetaMask’s warning: “This signature could potentially perform any operation” – heed that warning if you see it. Reject the signature and get outta there!